Description aircrack-ng
Aircrack-NG is an 802.11 WEP and WPA / WPA2-PSK.
Aircrack-NG can restore the WEP key as soon as it is captured enough encrypted packets in the AirODUMP-NG program. This part of the AIRCRACK-NG set determines the WEP key using two fundamental methods. The first method is by the PTW approach (Pyshkin, Tews, Weinmann). The default hacking method is PTW. It is done in two stages. At the first stage, Aircrack-NG only uses ARP packets. If the key is not found, then it uses all packages in capturing. Please remember that not all packets can be used for the PTW method. An important limitation is that the PTW attack currently can crack only 40 and 104 bit WEP keys. The main advantage of the PTW approach is that very few data packets are required for hacking the WEP key. The second method is the FMS / Korek method. The FMS / Korek method includes various statistical attacks to disclose the WEP key and uses them in combination with bruthetification.
Additionally, the program offers a dictionary attack method to detect the WEP key.
For hacking the common wPA / WPA2 keys, only the word attack method is used. SSE2 support is enabled to significantly accelerate the WPA / WPA2 key. The "four-way handshake" is required for input. For WPA handshake, a complete handshake is made up of four packages. However, Aircrack-NG is able to work successfully even with two packages. EAPOL Packages (2 and 3) or packages (3 and 4) are treated as a complete handshake.
License: GPLv2.
AIRCRACK-NG Help
using:
AirCrack-NG [Options]<.cap / .ivs файл(ы)> General Options: -a
Aircrack-NG Guide
General options:
-a.
Bruthet's attack mode, 1 or WEP for WEP and 2 or WPA for WPA-PSK.
-E.
Select the target network based on Essid. This option is also required for hacking WPA if the SSID is hidden.
-b.
Select the target network based on the MAC address.
-p.
Set the number of CPUs used (available only on SMP systems). By default, all available CPUs are used.
If this key is specified, the status information is not displayed.
-C.
Combine these MAC addresses TD (separated by comma) into one virtual.
-L.<файл>
Record the key to the file.
-E.<файл>
Create ELCOMSOFT Wireless Security Auditor (EWSA) project file v3.02.
Static hacking options WEP:
Search only alphanumeric characters.
Search only binary coded decodent symbols.
Search Key number for Fritz! Box
-d.
Specify the key mask. For example: A1: XX: CF
-m.
Save only IV came from packages that match this MAC address. Alternatively, use -M FF: FF: FF: FF: FF: FF to use all and each IV, regardless of the network (it turns off the ESSID and BSSID filtering).
-N.
Specify the key length: 64 or 40-bit WEP, 128 or 104-bit WEP, etc., up to 512 bit lengths. The default value is 128.
-I.<индекс>
Save only IV, which have a key index (from 1 to 4). The default behavior is to ignore the key index in the packages and use IV regardless of it.
-f.
By default, this parameter is set to 2. Use a higher value to increase the brutex level: hacking will take longer, but more likely to success.
-K.
There are only 17 korek attacks. Sometimes one attack creates a huge false response that does not allow to find the key, even with a lot of IV. Try -k 1, -k 2, ... -k 17 to disable each attack.
-X or -x0
Disable Brutfors last KeyBytes (not recommended)
Include Bruthetification of the Last KeyByte (Default)
Include the bruthetification of the last two keybytes.
Disable multi-thread bruthent (SMP only).
Show ASCII key version on the right side of the screen.
This is an experimental attack of a single brutfors, which is followed by using when the standard attack mode fails with more than one million IV.
Use PTW (Andrei Pyshkin, Erik Tews and Ralf-Philipp Weinmann) attack (default attack).
-P.<число> or --PTW-Debug<число>
Debugging PTW: 1 Disable Klein, 2 PTW.
Use Korek attacks instead of PTW.
-D or --wep-decloak
Use WEP disclosure mode.
-1 or --oneshot
run only 1 attempt to hack the key with PTW
-M.<число>
Set the maximum number iv that use
Options hacking WEP and WPA-PSK
-w.
The path to the dictionary file for hacking WPA. Specify " - "For standard input. Lists of dictionaries:
WPA-PSK hacking options:
wPA hack speed test.
-r.<базаданных>
The path to the Airolib-NG database. You can not use with "-w".
Other options:
-H or --help.
Show certificate
-u or --cpu-detect
Provides information about the number of CPU and MMX / SSE support
Examples of startup Aircrack-NG
Use the provided word list (-w /usr/share/wordlists/nmap.lst), to try to crack the password in the captured file (Capture-01.Cap):
[Email Protected]: ~ # aircrack-ng -w /usr/share/wordlists/nmap.lst Capture-01.cap Opening Capture-01.cap Read 2 Packets. # BSSid Essid Encryption 1 38: 60: 77: 23: 11: B1: CB 6EA10E No Data - Wep or WPA Choosing First Network AS Target. Opening Capture-01.cap
In general terms, the theory and the process of attack well described the user in his articles "Attacks on wireless networks", so I will not focus on many theoretical moments.
I want to describe the most simplest Ways to carry out protection, but in more detail.
-one. Couple words from ourselves
I want to say that I am categorically against the abuse of similar actions. Although in major cities now, there are now SER "Unlimited Internet" rules (so my conscience is sleeping in peacefully), but still do not need to dirty and abuse, especially since it can get sideways, what I will write below ... otherwise same, I do not see anything reprehensible about it, and I think that such actions are equivalent to how to warm up in winter from a foreign battery)))I will not consider all sorts of nuances and pitfalls that can meet on the way, those who want - will figure it out, the rest will sleep at night :)
This is my first article, so you don't bother :))
So let's go!
0. Foreign basic software
There are many programs for this kind of action, but we will use the AirCrack-NG package, in which everything is already necessary for us. This program is being developed under Linux, although there is a version and under Windows, but as I understand it, it is not particularly supported and does not work much)))
We jump and collect the latest version available at the moment. rC3 (from 03/26/09):
Wget http://download.aircrack-ng.org/aircrack-ng-1.0-rc3.tar.gz.
TAR -ZXVF AIRCRACK-NG-1.0-RC3.TAR.GZ
CD Aircrack-NG-1.0-RC3
Make
Make Install
UPD.
If you do not want to bother with source, then it is possible to download Aircrack-NG from the repository of your distribution. For example, in Ubuntu 8.10 repositories, the RC2 version is currently available, which can be downloaded and installed using the command:
Sudo APT-Get Install AirCrack-NGAlthough developers recommend using the latest version, because It has a lot of errors and many improvements have been fixed.
1. We collect information
First you need to transfer our Wi-Fi card to MONITOR MODE modeIn my case (with MADWIFI-NG driver) this is done like this:
Sudo WLANCONFIG ATH0 Destroy
Sudo WLANCONFIG ATH0 CREATE WLANDEV WIFI0 WLANMODE MONITOR
Now we will need a program to monitor all wireless networks within the radius of our Wi-Fi adapter. Personally, I like to use Airodump-NG from the previously formerly AIRCRACK-NG software package.
Run AirODUMP indicating the required parameter - the name of the interface (in this case, ATH0):
Sudo Airodump-NG ATH0
What do we see? Our card switches from the channel to the channel and displays all activity within reach. In the upper half, the discovered access points are shown in the lower customers detected (in this case, 3 clients were found, none of which is not connected anywhere):
It only looks like it seems that the nameplate looks incomprehensible, in fact everything is simple, here are the basic meanings that we are interested in:
- BSSID - Mac access point address
- PWR. - Signal level
- # Data. - the number of caught packets with data
- Ch - channel numbers on which is the access point
- MB. - Data transfer rate
- ENC. - Encryption algorithm
- Cipher. - type of encryption
- Auth - type of authorization
- Essid. - Access point name
- Station - Mac address client
- Probes. - Network names with which the client tried to connect
2. Choose the sacrifice: D
So what do we have? To act further, we need to choose our victim ...It should be noted that the signal level is a very important criterion. If the signal is below 5-10, then nothing good will not come out of the forefare with this network ...
For the next step, we look at the encryption algorithm (ENC):
- OPN. - Network without encryption ... It's nice of course, but not interesting :)
- WEP. - Network with WEP encryption ... In fact, it is that these networks represent the greatest interest for us.
- WPA / WPA2. - Do not believe! networks with WPA / WPA2 encryption :)))
3. Hi WEP!
I will not describe how to cope with SSID CLOAKING, MAC Filtering and other possible obstacles, it is enough to read the article N3M0 or AIRCRACK documentation, so I will go right away.Not linked in subtleties, hacking the WEP network comes down to the collection of sufficient number of packets, so you can simply sit and patiently wait until the desired amount is scored itself, but if there is no activity between the access point and the client, then we can see so week ... Therefore Will be generated not Without our help :)
So proceed to:
Next is an example taken from the site aircrack-ng.org. A network with the name (Essid) is Teddy, Mac address (BSSID) - 00: 14: 6c: 7e: 40: 80, and "Living" on the 9th channel. All this data is using AirODUMP (see paragraph 1 - "We collect information")
We start the AirODUMP aimed at the selected network located on the 9th channel, with the address of the access point, and the file name to which caught packets will be recorded:
Sudo Airodump-NG -C 9 --Bssid 00: 14: 6c: 7e: 40: 80 -w Output Ath0
Next in the new terminal, launch AirePlay to make friends with access point
AirePlay-NG -1 0 -e Teddy -a 00: 14: 6c: 7e: 40: 80 -H 00: 0F: B5: 88: AC: 82 ATH0Where:
-e teddy. - Name Name
-a 00: 14: 6c: 7e: 40: 80 - Mac Access Points
-H 00: 0F: B5: 88: AC: 82 - Our MAC
At the exit should receive:
aireplay-ng -3 -b 00: 14: 6c: 7e: 40: 80 -H 00: 0F: B5: 88: AC: 82 ATH0
Ideally at the exit should get something like this:
Saving Arp Requests in Replay_arp-0321-191525.cap
You Should Also Start Airodump-NG to Capture Replies.
Read 629399 Packets (GOT 316283 ARP Requests), Sent 210955 Packets ...
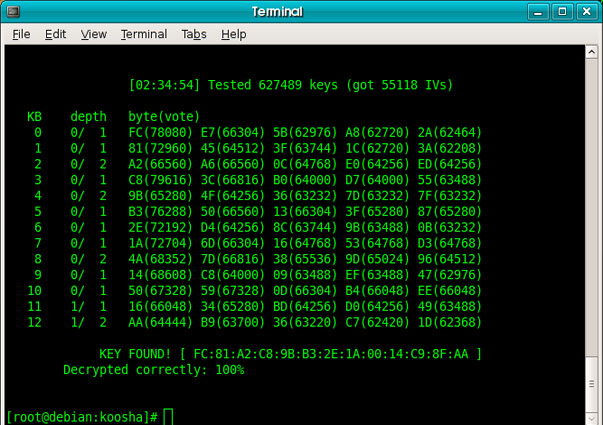
Now we switch to the window in which we have launched AirODUMP and contemplate the growing (with the proper signal) the number of packages. Usually there are plenty of 20 thousand packages for finding a 64-bit key.
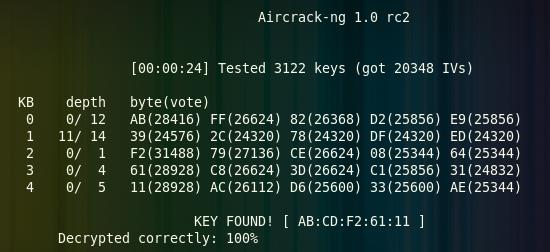
When the desired number of packages are collected, which shows the AirODUMP in the "# Data" column, launch the Aircrack-NG and enjoy the process of finding the password:
Aircrack-NG -Z Output * .cap
UPD.
Password in most cases is returned in a hexadecimal format, because Most routers translate the password in HEX each in their own way, so it is not possible to translate the values \u200b\u200bback to ASCII, although in some cases the initial password is written by side in brackets.
That's actually all. This password can be boldly to enter, only the colon is removed.
Under favorable conditions, absolutely nothing complicated :)
If the password has not been found, about which Aircrack will tell us, most likely you need to catch another packages, for example 40 thousand.
4. Inmplook WPA / WPA2
In this case, everything looks much easier, but it is much more complicated to the end result.To begin with, as usual, we launch Airodump aimed at the selected network ...
In the case of WPA / WPA2, the package collection does not work to move from the place. We need a client connected to the network, and even more accurately, we need to catch the moment the client's connection to the network. If the client is not, then we sit and wait ...
If the client is already connected, run AirePlay and break it with authentication, thereby causing it to connect it again:
Aireplay-NG -0 1 -A 00: 14: 6C: 7E: 40: 80 -C 00: 0F: B5: FD: FB: C2 ATH0Where:
-a 00: 14: 6c: 7e: 40: 80 - Mac Access Points
-C 00: 0F: B5: FD: FB: C2 - Mac client
And we get at the exit:
11:09:28 Sending Deauth to Station - Stmac:
Ideally, we must get the so-called. Handshake, what we will notify the Airodump again, displaying the right message in the top row "WPA Handshake: 00: 14: 6c: 7e: 40: 80".
If this happens, we use AirePlay again.
When Handshake is caught, launch Aircrack, but this time using the dictionary:
Aircrack-NG -W Password.lst -b 00: 14: 6c: 7e: 40: 80 Output * .cap
In this case, the result directly depends on the presence of the desired password in our dictionary, so our chances are directly proportional to the size and quality of our dictionary ...
Dictionaries can be easily found on the Internet, plus the Aircrack-NG archive is already small :)
5. A few words about protection
Several tips for those who categorically do not want to let outsiders to their feeder:- do not use WEP, and completely switch to WPA2 and more advanced protocols and add-ons over them
- do not use the minimum allowable password, the longer the better
- use a unique password, title and lowercase letters ...
- no dates (for example, all DDMMGYD format dates from 01/01/1950 to 01.01.2010 are moved per minute)
- use SSID CLOAKING and MAC Filtering, although in a little, but will help
6. Conclusion
That's it seems to be all ...These were the simplest ways to get around and strengthen protection, but even they do not always work.
For those who want to learn more, I advise you to visit the site
Nowadays, wireless networks are used more and more often, already in every home where there is an Internet, there is a router for distribution WiFi on mobile devices And other gadgets. Internet and WiFi have become an integral part of our life. But the question of the safety of such networks remained. As history shows, people have always found ways to hack the network, and the excellent confirmation is the WEP protocol, which is granted literally in a few minutes, even in the absence of users connected to the network.
But it seems that people are even less commonly using WEP and protect their networks using more modern standards such as WPA and WPA2. But are they really safe? In this article, we will look at how to use the AIRCRACK-NG utility to test the security of WPA and WPA2 networks. You will see them weakness And learn how to protect yourself from hacking.
What is Aircrack-NG?
Aircrack-NG is a set of utilities for testing WiFi networks. It was developed by a group of specialists with information security and it includes several utilities to scan network, transmit packets to the network, interface settings and directly, password enumeration. Programs support WPA and WEP networks.
The AirCrak package includes a large number of utilities, but we will consider only the most basic:
- airodump-NG. - Scanning network and capture packages that were sent on the air;
- airmon-NG. - switching the network interface to monitoring mode to receive all packages that are online;
- wESSIDE-NG. - Utility for automatic hacking WEP uses an attack of type PTW;
- easside-NG. - utility for automatic hacking WEP with the help of a keys based on initialization vectors;
- besside-ng. - automatic hacking WEP networks and handshake interception for WPA;
- airolib-NG. - utility to manage the list of access points and passwords;
- airbase-NG. - Universal utility for performing various attacks on WiFi network, is in development;
- tkipTun-NG. - utility for hacking WPA TKIP;
- airDecap-NG. - utility to decipher the intercepted traffic, it works only if there is a key;
- airdrop-NG. - performs user deautentication;
- aireplay-NG. - Allows you to generate traffic inside the WiFi network.
In this article we will use only some of these utilities. Namely Airodump, Airmon, AirCrHack and Besside for an automatic hacking attempt.
How will the attack work on WPA / WPA2?
As I said the encryption protocol wireless networks WPA also has its shortcomings. But most of them exacerbate the user. If you do not consider the recently open vulnerability in WPA TKIP, then all other problems arise due to a weak password.
For our test attack we will use your own network. It is assumed that you are not connected to it. Consider what is the essence of the attack. In order to connect to the network, each client must pass the authentication process with the router. I will not go into details, but there are four authentication on the MAC address, key and random numbers between the client and the router, if we intercept them, you can already try to sort out the appropriate password on the local computer.
The essence of the method is that the speed of extinguishing on the computer will be much faster than with manual check, it will reach up to 1000 passwords per second, and when using a very simple and expected password, you can quickly go through it.
First we will transfer the device to the monitor mode using AirMon-NG, then we will intercept all packages from this network using AirODUMP-NG until we find a handshake, then you will leave the dictionary password using the Aircrack. And now we turn closer to practice and consider how easy it is to go through your password if it is simple enough.
How to use Aircrack-NG to hack WPA
sudo Apt Install AirCrack-NG
And in Red Hat / CentOS:
sudo Yum Install Aircrack-NG
Windows You will have to download the installer from the official site. After installation, the first thing you need to do so that nothing bothered us. To do this, disconnect all the services that manage WiFi and the more turn off the WiFi network if you are connected to it. If NetworkManager is running, you need to turn off:
sudo SystemCTL Stop NetworkManager
I assume that you have already installed all the necessary drivers and you are ready for work. First, see the interfaces connected to the system:
sudo LS / SYS / CLASS / NET /
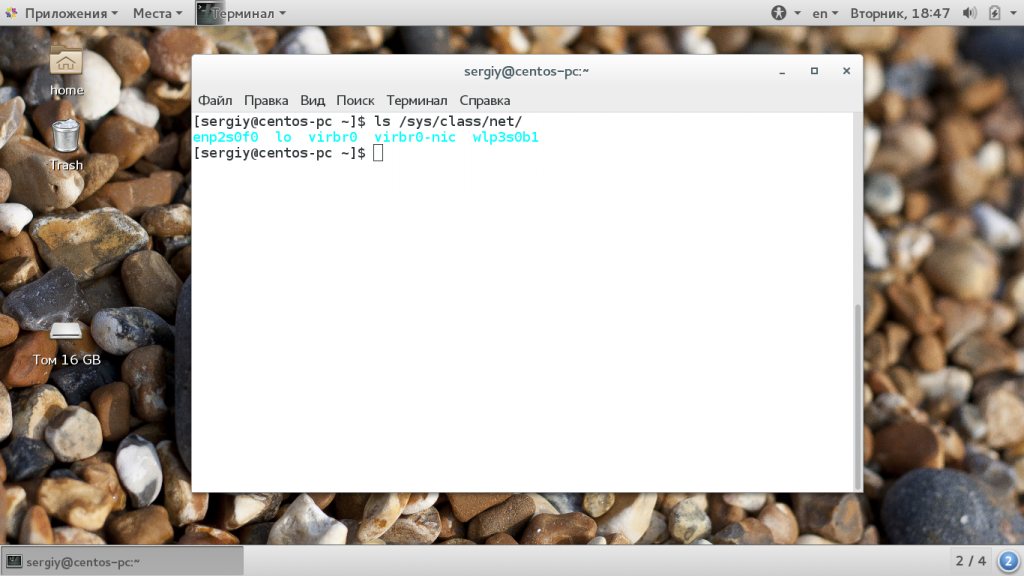
Usually, the name of the wireless interface begins on w, for example, WLP3S0 or WLAN0. I have it WLP3S0B1. We need to translate the WiFi network interface into monitoring mode. In this mode, it can capture all packages that fly online and even if they are not addressed to him. In general, the interface and so captures all the packages, but on the program level all packages that are not addressed to this computer are shifted, now they will not be filled. Next is the Aircrack-NG instruction.
To do this, use the AirMon-NG utility. She needs to transfer the Start command and the interface name:
sudo Airmon-NG Start WLP0S0B1

After that, a virtual interface will be created that works in the monitor mode in the second column displayed its name, I have this WLP3S0B1MON, although often it is called simply MON0. If any programs will interfere with the program will issue their names and PIDs:
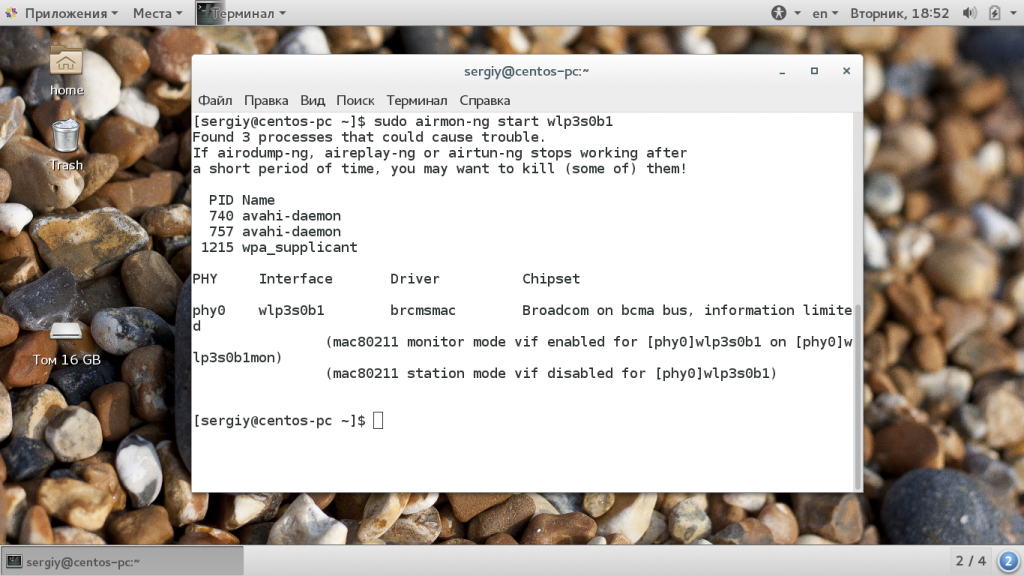
They must be completed using Kill. Next, we need to scan the broadcast and find our network that we are going to test. To do this, use the AirODUMP-NG command. In the parameters, it needs to transfer only an interface. Please note that you need to transmit a virtual interface that works in monitor mode:
sudo Airodump-NG -i WLP3S0B1MON
![]()
Almost immediately you will see your network because it is located closest. I have this mypublicwifi423. From the information provided, we will need its BSSID and a channel that can be found in the CH column. Then we will use the same utility, only now it is aiming it for our network so that she is not distracted by outsiders and caught everything we need.
We will set the channel using the -C and BSSID Router option using the -BssID option, and also point out the -W option where you need to save the intercepted packages for further processing:
sudo Airodump-NG -C 11 --Bssid 56: 0a: 64: 17: 5d: 33 -w /home/sergiy/Hack.pcap WLP3S0B1MON
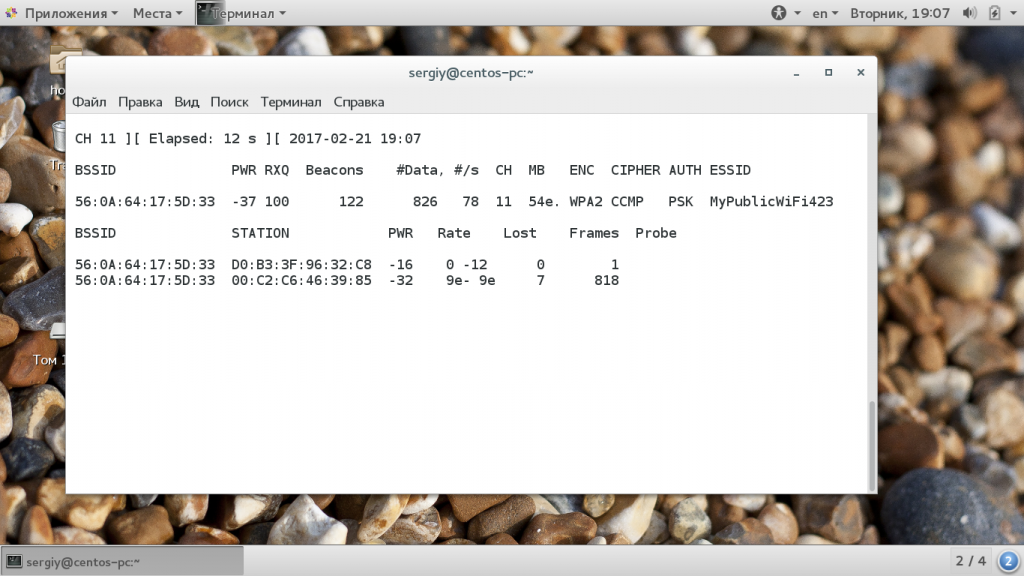
Do not close this terminal, now captures and how you can see two users are connected to our network. Their MAC addresses are in the Station column. If now one of them turns off and connects again, then we get the data necessary for further hacking.
We can do it with your devices, but in the real network of hacker will not have such an opportunity, so we can forcefully disable the client from the network using the AirePlay utility. If you transfer it the Deauth option, then it will send a broadcast message on behalf of the router, in which it will ask everyone to disconnect from the network. We only need to transfer the number of packages in the parameters to be sent and the BSSID router:
sudo Aireplay-NG --Deauth 10 -a 56: 0a: 64: 17: 5d: 33 WLP3S0B1MON
![]()
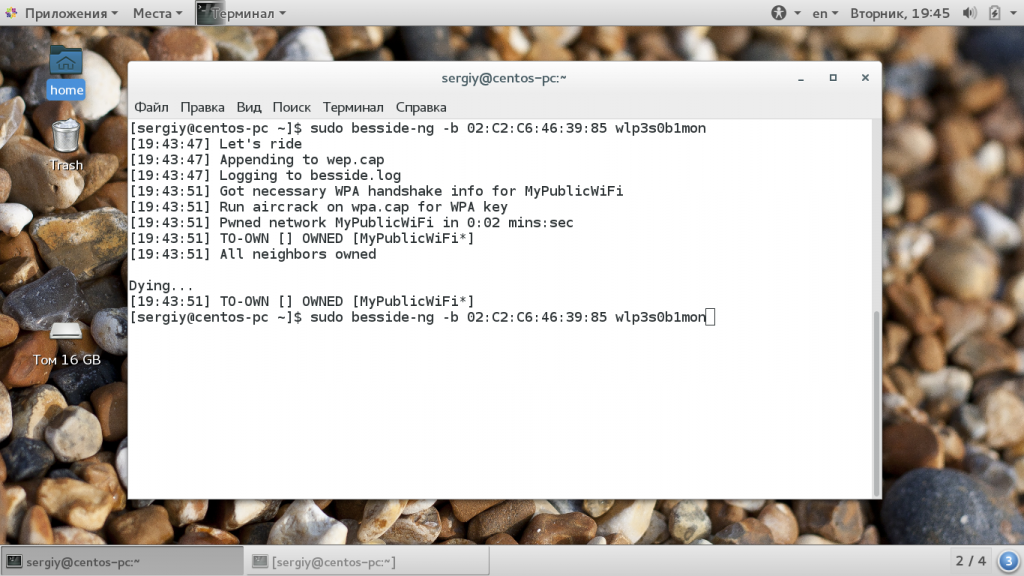
Immediately after that you will immediately see the post WPA Handshake: 56: 0a: 64: 17: 5d: 33 in the upper right corner of the terminal. You can use and easier way to get Handshake. The Besside utility allows you to perform all actions automatically you only need to transfer the BSSID router and the monitor interface:
sudo Besside-NG -B 02: C2: C6: 46: 39: 85 WLP3S0B1MON
The stage associated with the work in the real network is completed and we can only go through all possible passwords in the dictionary. Next, consider how to use Aircrack-NG for passwords.
The dictionary is an ordinary text document with a list of possible passwords. You can make it yourself. The command will look like this:
$ sudo aircrack-ng -b BSSID_Marshrutizator -W Path_K_Slovary intercepted_pakets
sudo Aircrack-NG --Bssid 56: 0a: 64: 17: 5d: 33 -w / Home / Sergiy / Words /home/sergiy/Hack.pcap-01.cap
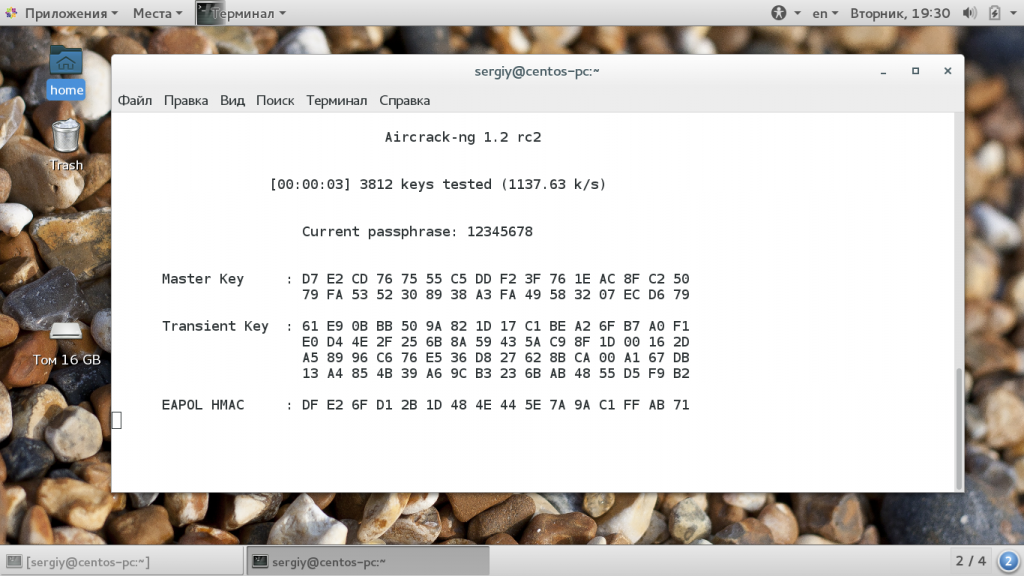
![]() As you can see, Aircrack-NG WPA2 PSK can quickly be hacked. The speed of passwords reaches thousands of options per second, which means that only a few minutes will go to the brute force up to 100,000 passwords. And this is on the usual, budget laptop. On a more powerful gland, the AirCrack NG will be much faster.
As you can see, Aircrack-NG WPA2 PSK can quickly be hacked. The speed of passwords reaches thousands of options per second, which means that only a few minutes will go to the brute force up to 100,000 passwords. And this is on the usual, budget laptop. On a more powerful gland, the AirCrack NG will be much faster.
Therefore, never use simple passwords consisting of numbers only if you add at least one letter or symbol, then reduce the chances of hacking several times.
conclusions
In this article, we considered how to use the Aircrack-NG program for hacking WPA and WPA2 networks. Remember that hacking of other people's systems is a crime for which you can suffer criminal liability, so use the above methods described only to test your networks. This Aircrack NG manual is intended only for review, so that users can understand how dangerous use simple passwords.
Consider the AirCrack-NG - the best software In the world to hack Wi-Fi, and let's start with some foundations that is included and how to use all this.
First of all, AIRCRACK-NG is not just a tool, but rather a set of tools for editing and hacking Wi-Fi networks. In this set there is a tool called Aircrack for hacking passwords, but to get to hacking, we need to make several steps with the help of other tools. In addition, Aircrack-NG is able to perform DOS attacks and much more.
So let's start with AIRCRACK-NG set!
Short note
nG means "New Generation", so the AirCrack-NG replaces the old Aircrack set, which is no longer supported.
Step 1: IWConfig
Before you start working with Aircrack-NG, we must make sure that Backtrack Determines the wireless adapter. We can do it in any Linux system by typing:
· Bt\u003e iveconfig

We see that BackTrack has identified the author's USB wireless card, and he says that the card supports 802.11bn that Essid is turned off, that it is in control mode, etc.
Well, now we are ready to start using Aircrack-NG.
Step 2: Airmon-NG
The first tool that we will look at and which almost never requires hack WiFi, is AirMon-NG, which translates our wireless card into an inadvertent mode (ed.: Monitoring mode). Yes, this means that our wireless card is connected to any!
Well, it is almost right. When our network card in monitoring mode, this means that it can see and receive all network traffic. As a rule, network cards receive only packets designed for them (which are determined by the MAC-address of the network adapter), but with the help of Airmon-NG, it will receive all wireless traffic, it is independently designed for us or not.
We can run this tool by entering AirMon-NG, Action (Start / Stop), and then Interface (MON0):
· Bt\u003e Airmon-NG Start WLAN1

AirMon-NG provides some key information about our wireless adapter with a chipset and driver. Most importantly, note that it has changed the designations of our wireless adapter with WLAN1 on MON0.
Step 3: AirODUMP-NG
The next tool in the Aircrack-NG set, which we will have to use, AirODUMP-NG, which allows you to intercept the packages of our specification. This is especially useful when hacking passwords.
We activate the Airodump-NG command input tool and renaming the monitoring interface (MON0):
· Bt\u003e Airodump-NG MON0

As can be seen in the screenshot above, the AirODUMP-NG displays all AP (access points) within the range from their BSSID (MAC addresses), their power, number of signal frames, number of data packets, channel, speed, encryption method, type used cipher, Used authentication method and finally Essid.
For our purposes of hacking WiFi, the most important fields will be BSSID and the channel.
Step 4: Aircrack-NG
Aircrack-NG is the main application from the Aircrack-NG set, which is used to hack passwords. It is able to break WEP using statistical methods and crack WPA and WPA2 in the dictionary after capturing the WPA handshake.
Step 5: Aireplay-NG
AirePlay-NG is another powerful tool in our Aircrack-NG arsenal, and it can be used to generate or accelerate the traffic point traffic. This is especially useful in such attacks as Deauth attacks, when you hit all access points, attacks on the WEP and WPA2 password, as well as for ARP injections and playback attacks.
Aireplay-NG can get packages from two sources:
Direct stream (broadcast) of packages or
Pre-captured and saved in the PCAP file
The PCAP file is a standard file type associated with package capture tools such as LIBPCAP and WINPCAP. If you have ever used Wireshark, then most likely worked with PCAP files.
Aircrack - The best performance and quality of work program used for hacking Wi-Fi. Question: "How to use Aircrack?", More and more people are interested in the circle of ordinary users. With all its advantages, Aircrack-NG is ported to many different platforms - such as Zaurus, Maemo and, which is particularly pleased with the iPhone users. And among those supported operating systemsThe most popular: UNIX, Mac OS X, Linux and Windows.
In a fairly large number of users, certain problems arise using AirCrack, for this reason, it was decided to write a guide to the cracker. Although the AirCrack is not really difficult to use, the only complexity can be considered a fairly large English-language interface.
How to use the aircrack program
Two main encryption methods are used for Wi-Fi: WPA and WEP..
If the grid that you came across has a WEP encryption method (more "outdated"), then you can hack it almost for sure! Only the signal is desirable, there must be power at least above the average (otherwise the process will be unnecessarily long).
The essence of hacking with the Aircrack is as follows:
- First you need to "catch" quite a lot of packages containing IVS key. More specifically - they will need no less than 10,000. It is better - more (with 20,000 hacking WEP is almost guaranteed).
- To determine the password received in the Dump file, you will need to run in the AirCrack on the bust. It follows this (for example, we will analyze the GUI version).
- We are looking for the Archive of the program AIRCRACK-NG GUI file and launch it.
- The main program window opens. We are looking for a path to the FileNames path to a dump with saved keys.
- Low below, specify the program that in this dump password is encrypted using the WEP method. Determine the key length in 128 or in 64 (maybe you have to try different variants - If the password does not exist at 64, it will be possible to try at 128).
- The USE WordList cell is needed in order to search by the dictionary, there is no need to check there. But USE PTW Attack is a bust in all possible signs. Here and put a tick, then click Launch.
- A command line will appear, it will be necessary to select the name of the grid for hacking and put the number from 1 to 4 - depending on which number this program has determined the name of your grid from this dump. In the event that all parameters are delivered correctly, the bust will successfully start.
It usually lasts about 2 minutes. If you managed to collect enough IVS keys in the dump, then you will receive a password, but not in the form of a "clean" set of characters, but with colon. For example, so: " 01:19:42:24:58 ". In this case, the real password is 0119422458.
